Large banks, financial institutions and other financial services (FS) players across the European Union have been urged to take part in a voluntary training exercise ahead of the EU’s new Digital Operational Resilience Act (DORA), which is coming into force early next year.
Banks across all EU member states, as well as insurers, asset managers and other financial firms have been invited by the European Supervisory Authorities (ESA) to join the mass-testing exercise, which is scheduled to take place next month. An exact date has not been set yet.
The test is co-coordinated by the European Banking Authority (EBA), the European Insurance and Occupational Pensions Authority (EIOPA) as well as the European Securities and Markets Authority (ESMA).
Handing over contracts
Firms that agree to take part will be asked to hand over the agreements they have in place with any ICT third party providers they work with.
Starting in May, participating firms will be expected to forward their registers to the ESA through their relevant national watchdogs before the end of August.
Providing this information is an important part of DORA because, once in effect, financial firms will be required to register any contractual arrangements they have with third party ICT firms.
In the invitation letter to firms, which was sent last week, the ESA explained they plan to offer extensive help, support and guidance to firms to help them create and maintain a register.
The regulator indicated it will soon propose a standard format and data quality testing will become an important part of the process.
Firms will then be asked to hand over their registers to the ESA through their relevant national watchdogs, most likely between early July and late August.
DORA is among several recent and emerging regulations in the EU, created to enhance and standardise requirements for enterprise cyber resiliency.
The rules are specifically for financial entities operating across the EU 27 — including banks, insurance companies, credit agencies and more — and third-party service providers that serve them.
‘Oversight’ framework
DORA will come into force on January 17 of next year. Ahead of the January 2025 deadline, the European Commission formally adopted a number of DORA stipulations in February.
The EU’s executive body issued a whole set of secondary legislation that set out detailed, technical rules specifying some of the key provisions of DORA.
Firstly, it has now been confirmed that DORA will introduce an ‘oversight framework’, which did not exist under pre-existing outsourcing regulations.
What does DORA cover?
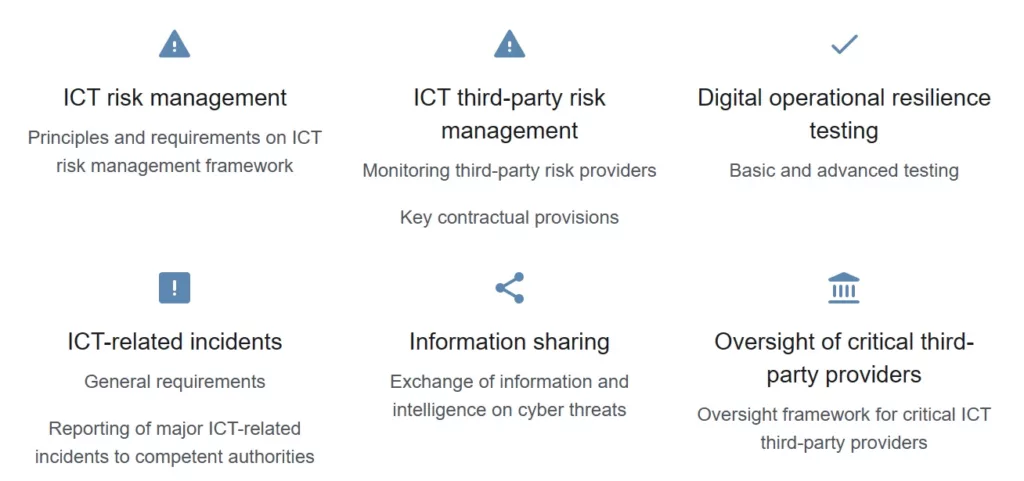
ICT third-party service providers that are designated as ‘critical’ will be made subject to regulatory scrutiny, largely overseen by the ESA, which are the above-mentioned ESMA, EBA and EIOPA.
This approach allows the ESA to investigate and inspect providers in relation to IT security, risk management and governance issues.
The framework also gives ESA the power to make recommendations and issue fines of up to 1% of the ICT third-party provider’s annual worldwide turnover.
Moreover, the EC also detailed the criteria “for the designation of ICT third-party service providers as critical for financial entities.”
In other words, it set out what ‘critical ICT providers’ are. In addition, the EU body also introduced a vast and fairly complex structure for oversight fees.
‘Two step’ approach
To determine whether an ICT third-party service provider is ‘critical’ for banks, insurance firms and other financial entities, the ESAs will use sub-criteria in a two-step approach assessment.
Firstly, the ESAs will take into account important ICT services and the diversity and number of financial institutions that use those services.
This is primarily done to “filter the population of ICT third-party service providers and identify the most critical ICT third-party service providers.”
After this ‘first selection’ of ICT third-party service providers, a further in-depth analysis will be carried out that focuses on a range of sub-criteria.
So far, the EC has not set out these standards but has hinted that, in some cases, it will be left to individual member states to fill these gaps.
Pressure tests
A host of industry insiders have warned that many banks and finance firms do not fully realise they could face substantial fines and penalties within a year if they do not significantly expand or adjust their testing capabilities.
In fact, DORA will require the creation of new pressure tests and other critical testing infrastructure.
Banks, insurers and other financial services firms are therefore urged to urgently review and revamp their testing strategies as DORA is “not just a fire drill”, according to Kris Lovejoy.
Lovejoy is global security and resilience leader at information tech services multinational Kyndryl, the spin-off of IBM’s infrastructure services business in 2021 and a major developer of IT security testing solutions.
“Financial services firms and other entities that will must strengthen or build pressure test and implement the critical systems and protocols that will protect both operational and personal data from adverse manipulation, destruction or theft,” she stated.
“If they don’t, they’ll be subject to sanctions and penalties, up to and including the C-suite and board of directors, in addition to operational and reputational damage,” Lovejoy added.
With regards to January 17 next year, when DORA takes effect, she said “next January may seem like a distant target. But in the complex world of financial services information and communication technology, one year is hardly enough.”

“Firms must strengthen pressure test and implement critical systems and protocols.”
– Kris Lovejoy
That sentiment is echoed by Fabio Colombo, head of Global Cybersecurity for financial services at Accenture.
Milan-based Colombo said in agreement that banks and other finance firms will need to update and change their testing capabilities, operating procedures and risk if they wish to be fully compliant with the EU’s new DORA framework.
DORA will also require operational reviews, system evaluations, more training and frequent audits, he added.
Colombo’s observations are not new. QA Financial stated in 2022 in a report that operational preparedness efforts needed to be stepped up in order to ensure that all participants in the financial system have the necessary safeguards in place ahead of DORA.
In conjunction with Accourt Payment Specialists and Reed Smith, Expleo and QA Financial gauged the prevailing sentiments of 39 traditional and challenger banks, asset managers, insurers, payment firms and other Fintechs in the UK and EU.
Regular testing
For banks, insurers and finance firms, regular testing of ICT systems to evaluate strengths and identify vulnerabilities “will now become of paramount importance, as results and subsequent plans to address any areas of concern will need to be shared with the relevant competent authorities,” Lovejoy said.
She stressed that, under DORA, financial entities will also be required to undertake annual basic testing, such as vulnerability assessments and scenario-based testing, whilst those considered to have a critical role in the financial system and their ICT providers will also need to undergo additional threat-led penetration testing every three years.
“Financial entities will be required to undertake annual basic testing, such as vulnerability assessments and scenario-based testing,” Lovejoy explained.
Finally, she pointed out that DORA will require internal audit functions to review and potentially augment all their current plans and programs, as these will now need to pinpoint potential risks to financial entities via third-party ICT providers.
“This means that internal audit functions should be challenging their established risk-identifying process regularly, maintain a register of information related to all contractual agreements, and report to regulators annually,” she noted.
Stay up to date and receive our news, features and interviews for free
Our e-newsletter lands in your inbox every Friday. Sign up HERE in one simple step.
Lovejoy expects that firms may opt to outsource their reporting obligations to a third-party, but “ultimately remain responsible for compliance with obligations under DORA.”
“The application of DORA safe protocols should not be considered as a fire drill, as proper planning for critical cyber activity requires considerable and regular training, senior management support and properly prepared security operations teams to be most effective,” she warned.
In summary, the new framework means a major change from the current regulatory approach.
Prior to DORA, the EU operational resilience and cybersecurity risk management governance model for financial firms was based on a disparate collection of national rules, guidelines, and practices that did not empower EU financial supervisors to impose uniform requirements on FEs nor to assess the risks arising from their dependence on TSPs.
“DORA tackles these disparities and uneven national regulatory or supervisory approaches,” Lovejoy concluded.
LAST WEEK
DO NOT miss coverage of our recent conferences in Chicago and Toronto

READ MORE




